IT security software provides protection to businesses’ computers or networks. It serves as a defense against unauthorized access and intrusion in such a system. It comes in various types, with many businesses and individuals already using some of them in one form or another.
Many businesses are using PCs, networks, and servers to store their organization’s vital information (which, in most cases, contain private and financial information of clients and customers) and manage their core operations. This stresses the importance of having a good and reliable security system in place.
In this article, we’ll go beyond the definition of IT security software to get a better understanding of what this software does, what is it for, and how it can give value to your organization. We’ll discuss the purpose of IT security software and these other key points:
IT Security Software Guide Table of Contents
Importance of drawing the focus on cybersecurity challenges
With the emergence of more advanced technology, cybercriminals have also found more ways to get into the system of many organizations. Since more and more businesses are now relying their crucial operations on software products, the importance of software security assurance must be taken seriously – now more than ever. Having reliable protection such as IT security software is crucial to safeguard your computing environments and data.
It is not just the government or big corporations that become victims of cyber threats. In fact, small and medium-sized businesses have increasingly become targets of cybercrime over the past years. SMBs are also used as a gateway by cybercriminals to penetrate larger businesses using their direct and indirect business relationships. An estimate of half of the small businesses suffers from cyber attack, resulting in business closures within six months according to the U.S. Securities and Exchange Commission. It can be quite costly for a business as you can see from the visual below. Hence, cybersecurity is a concern that the entire business community shares.
Source: CB Insights
What’s even more alarming is how organizations not only have to protect their system from external factors, but they have to secure it internally as well. Some of the biggest cybersecurity threats are the result of mistakes and misuse of the organization’s own employees and contractors. The 2018 Verizon Data Breach Investigation Report reveals that 68% of data breaches take months or longer to discover – a significantly long time for these threats to go undiscovered.
At the 2018 Cyber Security Business Insight Conference, panelists concluded that employees remain as one of the biggest threats to their system security. This appears to be justified as another research shows 24% of UK employees admit to intentionally revealing and sharing confidential business information outside their organization, such as new and previous employees, and even competitors.
Types of IT Security Software
How does IT security software work? In essence, it detects and, in some cases, mitigates security attacks in your system. Since there are various types of security attacks, there are also various types of security products to target each one of them. Here are some of the most popular ones:
- Firewall. The over-arching term “firewall” refers to the specialized defense systems for a single computing device or computer network. It filters data that enters or leaves a computer or network by blocking or restricting network ports from viruses and hackers. It also serves as a barrier between a trusted and untrusted network by only allowing traffic that’s defined by the firewall policy to enter the network. Serving as your computer’s first line of defense, this utility also comes in even more various types such as proxy firewall, stateful inspection firewall, unified threat management (UTM) firewall, next-generation firewall (NGFW), and threat-focused NGFW.
- Antivirus. This software utility is designed to prevent, search, detect and remove malicious software or malware such as viruses, worms, scareware, and Trojans. With the constant onslaught of new viruses, these programs are often updated to enable the system to check new threats. While vendors vary in their offerings, some of its basic functions include scanning files and directories for suspicious patterns, scheduling automatic scans, scanning of a specific file of your computer, CD, or flash drive at a given time, removing any detected malicious codes or infected files, and providing you an overview of your computer’s health.
- Spyware detection. Spyware, also called malware and adware, are software programs installed on your computer without your consent. Anti-Spyware software is used to detect their presence on your computer or network and prevent or remove their installations. Removing them is crucial because they “spy” and record your personal information from your computer, as well as computing behaviors such as your documents, web browsing, and keystrokes. This can tailor the advertising on your computer, change its configuration, and even send your personal details to another remote computer.
- Password protection. One of the highly used methods to prevent unauthorized access to a computer, file, folder, and system is protecting it with a password. The challenge of having a password lies in human memory. In most cases, many people use an easy-to-remember password such as birthdays and family names (and in many cases, the word “password” itself) which also makes it easy to guess for cybercriminals. Furthermore, many reuse the same password across various platforms which exposes risks to all your accounts even when only one is compromised. On the other hand, a unique, hard-to-guess password in each account is hard to remember. This is where password protection security comes in handy in generating strong passwords and storing them securely.
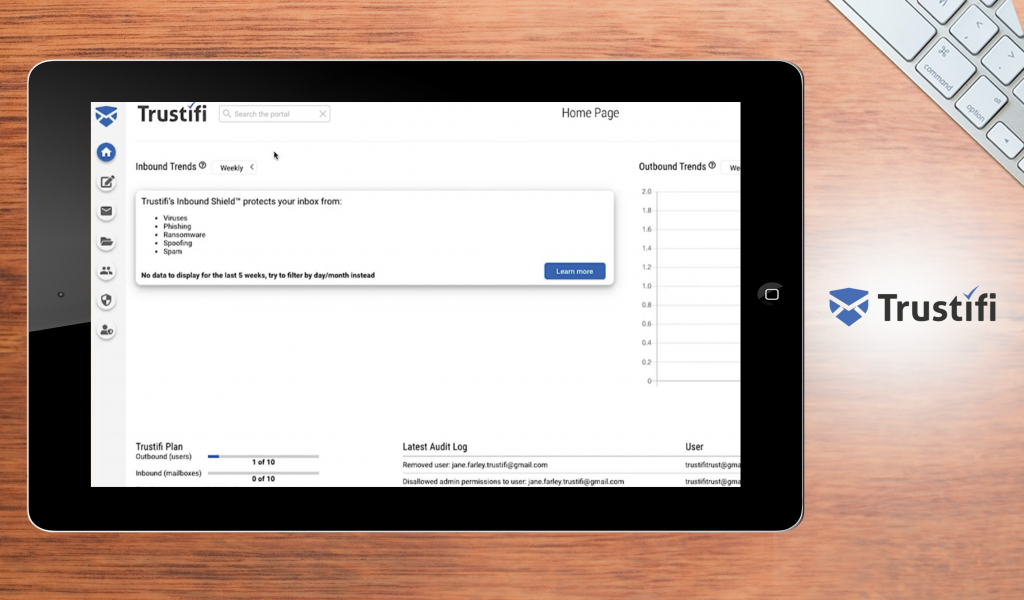
Trustifi helps protect your organization from the broadest types of online attacks, either basic or advanced.
Features of IT Security Software
What does IT security software do? Here are some of the key features of the security software:
- Automatic updates. This ensures you don’t miss any updates and your system is the most up-to-date version to respond to the constantly emerging new cyber threats.
- Real-time scanning. Dynamic scanning features make it easier to detect and infiltrate malicious entities promptly. Without this feature, you’ll risk not being able to prevent damage to your system before it happens.
- Auto-clean. A feature that rids itself of viruses even without the user manually removing it from its quarantine zone upon detection. Unless you want the option to review the malware, there is no reason to keep the malicious software on your computer which makes this feature essential.
- Multiple app protection. This feature ensures all your apps and services are protected, whether they’re in an email, instant messenger, and internet browser, among others.
- Application-level security. This enables you to control access to the application on a per-user role or per-user basis to guarantee only the right individuals can enter the appropriate applications.
- Role-based menu. This displays menu options showing different users according to their roles for easier assigning of access and control.
- Row-level (multi-tenant) security. This gives you control over data access at a row-level for a single application. This means you can allow multiple users to access the same application but you can control the data they are authorized to view.
- Single sign-on. A session or user authentication process that allows users to access multiple related applications as long as they are authorized in a single session by only logging in their name and password in a single place.
- User privilege parameters. These are customizable features and security as per individual user or role that can be accessed in their profile throughout every application.
- User-specific data sources. This enables you to build a single application that, depending on the user, accesses various data sources. It is the same with row-level security but on a database tier.
- Application activity auditing. Vital for IT departments to quickly view when a user logged in and off and which application they accessed. Developers can log end-user activity using their sign-on/signoff activities.
Benefits of IT Security Software
Why use IT security software? The real advantages of IT security software solutions directly correspond to the consequences of not having one. At some point, even the most tech-savvy users may download some form of malware or become victims of online scamming and identity theft. The internet is not a secure place and with more and more operations managed by SaaS solutions, prioritizing your entire organization’s protection is imperative.
- Prevention of viruses, spyware, and identity theft. Hackers are finding trickier ways to create viruses that may pose as anti-virus software, email from a friend, or imposter bank websites. Once they infect your computer, they can drastically slow down your processing speed, delete critical data, and damage your computer or network systems. Identity theft and spyware can also be prevented by using the software to safeguard confidential personal information such as passwords, financial data, credit card numbers, and social security numbers of your system’s users. In fact, 80% of cyber attacks are caused by weak or stolen passwords, hence, they must be secured carefully.
- Protection of valuable information. Information is one of the most valuable assets of any organization. Hence, its protection is a vital part of your IT infrastructure. Loss of critical information caused by data corruption can be detrimental to your business. Furthermore, MasterCard International Inc. and Visa USA require data encryption to allow businesses to operate in order to protect customers when using their credit cards. Encryption and limiting access to sensitive information are only some of the aspects that are handled by information-technology security.
- Ensure compliance. Many IT departments need to comply with legal, insurance, and industry restrictions to perform the management and transmission of data. Some of the most notable regulations to take note of includes FIPS, PCI/DSS, Gramm-Leach Bliley, HIPAA, and FISMA. Security software provides the encryption they require for compliance whenever your file is accessed, shared, circulated across various devices, and sent from or received in your system.
- Security for clients. Give your clients peace of mind by making them aware your system is protected. At a time where cybersecurity is crucial, this benefit potentially increases your sales and marketability. The security and safety of their sensitive personal information are some of the customer’s primary concerns which make them hesitant to share their information and make transactions online. With that, having security solutions assures your customers that their information is safe with you. The best-industry practices give you rewards with an increased number of customers, higher sales, and a sound market reputation.
- Reduced costs of development. Implementing a security solution early on prevents you from high costs along the way. While it’s never too late to install security software in your system, the sooner you have it, the better. If you choose to do it later, you’ll have more codes to modify. Inadvertent data loss and retrieval may also cause you a huge sum of money and amount of time when not prevented. In 2016 alone, the cost of cybercrime in the global economy reached upwards of $450 billion. By 2019, it was expected to reach up to $2 trillion.
Buying Factors of IT Security Software
With the wide array of products available, choosing the right security solution for your organization can be challenging. Not one product is completely the same as another. Aside from understanding the definition of what is IT security software, these factors should be on top of your list before deciding to purchase an IT security system for your business:
- Layered approach to security. Protection alone is not enough to safeguard your system. Choosing software that has a layered approach closes any security gaps to identify potential threats and prevent them from causing further damage. The isolation and identification of threats must be covered in all layers. This includes firewalls, malware scanners, local storage encryption tools, and intrusion detection systems.
- Compatibility with your system needs. Understanding your own IT setup, network specification, software installations, and the different types of equipment in your system is crucial to shortlist potential security packages to fit in your specific business environment. An example is the media encryption service which is essential for companies that use removable storage to block infected files from entering your network.
- Capability to cope with emerging threats. Cybercrime tech and tactics constantly evolve. If your system cannot respond to new threats, it won’t be of use to you and your system. Adapting and imposing protection against emerging threats should be a significant factor in choosing an IT security package. Check their software updates and patches if they are as innovative as the efforts of cybercrime.
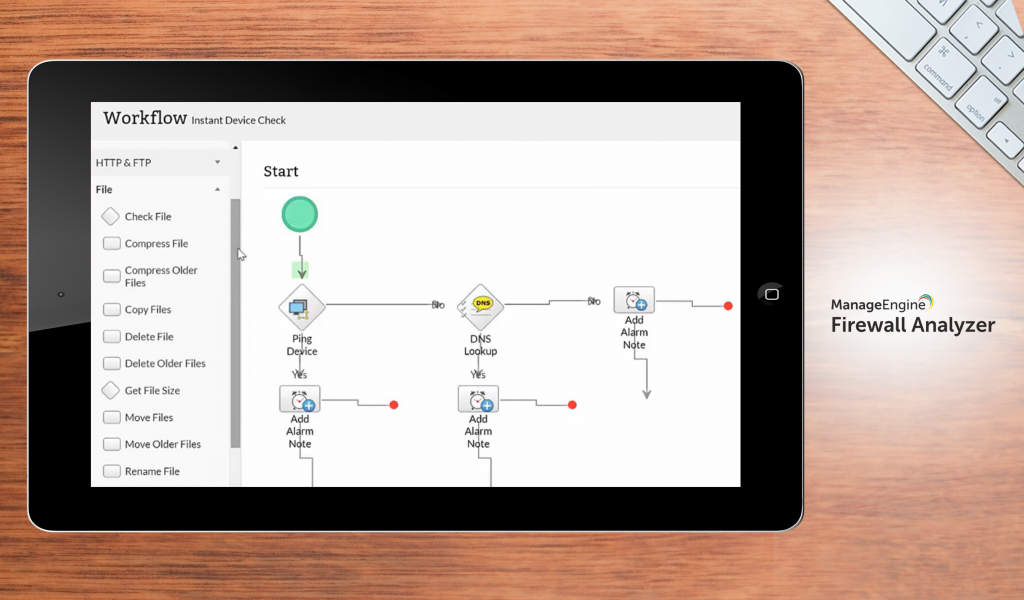
ManageEngine Firewall Analyzer helps you understand how your bandwidth is being used and lets you integrate with many other vendors.
Examples of IT Security Software
Since there are many types of information-technology security software products, we listed the top solutions you can check out for a head start. These examples of IT security software products offer a robust set of tools and features to match your cybersecurity requirements.
ManageEngine
ManageEngine Firewall Analyzer helps you comprehend how your bandwidth is being used, monitor traffic, and detect anomalies. You can get insights into network activity and threats and receive threat notifications, allowing you to prevent malicious attacks and keep your networks safe and optimal. It supports Check Point, Cisco, Juniper, Fortinet, Palo Alto, and other vendors. You may request a demo before asking for a quote.
BigID
BigID lets you understand your data, allowing you to make informed decisions about your business. With this modern data intelligence platform, you can discover, manage, and protect your business’ critical data. You may integrate it with AWS, Privitar, among many others, and with its use of machine learning, you can have efficient, consistent, and scalable data governance across the cloud and data centers.
Norton
Norton Security protects against viruses, spyware, malware, and other cyber dangers in real-time with advanced features like anti-theft and performance optimization. Other features include spam filtering, phishing protection, and a personal firewall. It uses a global intelligence network to discover new and potential cyberattacks, halting them before they escalate. It works on Windows 7 and later, macOS 10.10 and later, and Android 4.1 and iOS 8 and later.
Cloudflare
Cloudflare specializes in Content Delivery Network (CDN) service designed to protect websites, mobile apps, SaaS services, APIs, and other internet-connected assets. It is one of the world’s largest cloud network platforms and is used by over 12 million domains, helping reduce website latency as well. Cloudflare’s enterprise-grade web application firewall (WAF) continually detects and deters new possible threats.
Avira
Avira Antivirus Server provides maximum server protection with minimal impact, easy scalability regardless of server count, and zero-cost maintenance. It gives you network, on-access, and on-demand protection, and has a robust anti-virus engine. It also offers a structured UI that enables you quickly assess your server’s security. This product is only one of the over two dozen tools and solutions for homes and businesses offered by Avira Operations.
Malwarebytes
Popular on-premises malware protection for Windows, macOS, iOS, and Android, Malwarebytes looks for and removes threats like ransomware, spyware, and adware, using modern anti-spyware, anti-rootkit, and anti-malware technology in removing viruses in real-time. It also protects itself from unauthorized alterations and remote file locking by cybercriminals. However, there are no automatic or scheduled scans in the free version.
Kaspersky
Apart from antivirus software, Kaspersky Lab offers endpoint security, password management, and device and app security controls. It is famous for products passing rigorous independent tests and a global team that uncovered the most sensational and notorious cyber weapons and threats. It has 400 million users worldwide, has the highest share of the European cybersecurity industry, and ranks third globally in consumer IT security software sales.
Trustifi
Trustifi protects your organization from the broadest types of online attacks, either basic or advanced, whether your teams are in the world. This cloud-native email security software offers an innovative cloud architecture that identifies the most sophisticated attacks and stops them dead on their tracks. You can integrate it with GoDaddy, Google Workspace, Check Point, and more. The price will depend on your company size and need.
Spiceworks
Spiceworks offers a free IT toolkit to manage, secure, and monitor systems, networks, and devices. It gives IT professionals real-time information on IP devices, switches, and servers, allowing them to monitor their network’s health. It keeps track of network devices, scans them automatically, detects threats, and protects websites and networks. Spiceworks provides real-time monitoring and alerts so users may quickly detect and resolve issues.
Webroot
Webroot SecureAnywhere protects endpoints from cyber threats that could harm cloud business infrastructures. Real-time intrusion detection software integrates predictive, machine learning, and cloud computing technology. It eliminates the need for constant virus definition updates by providing real-time visibility of infections on any network endpoint, from entry to automatic wiping. Thus, you have intelligent malware protection.
Bitdefender
Bitdefender is an antivirus for Mac, Windows, Android, and iOS. In addition to cybersecurity measures against viruses and malware, it offers privacy protection technologies for individuals, corporations, and governments. Its Family Pack provides content limits and parental controls, while its Internet Security Suite provides enterprise-level protection for online data. Despite its small size, it has powerful features tailored to your needs and devices.
AVG
In addition to protecting against viruses and malware, AVG AntiVirus Business Edition protects against hackers and other cyber dangers. It helps SMBs protect files, data, emails, networks, computers, and even mobile devices while also securing documents and files in a password-protected virtual disk on your device. It has a built-in shredder that securely deletes files and an anti-spyware capability that detects adware and spyware data collection.
Pricing of IT Security Software
What is the cost of IT security software? To give you an overview of how much you’ll invest in this system, we listed below the pricing plans of some of the leading solutions in the niche.
- ManageEngine ADSelfService Plus. Their pricing options start at a Free Edition for up to 50 domain users with no expiry date. For advanced features, users can look at the software’s Standard Edition and Professional Edition with annual subscription fees starting at $745 and $1,195 respectively for 500 domains.
- EventLog Analyzer. It has a free edition that supports up to five log sources. For paid plans, the annual subscription license for Premium Edition starts at $595 while Distributed Edition goes for $2,495.
- Glasswire. The device, data, and privacy protection software offers three pricing plans – Basic at $29 for one PC, Pro at $50 for 3 PCs, and Elite at $75 for 10 Pcs.
- Dhound. The threat detection solution for servers, apps, and cloud assets is available in three packages – Lite at $15/month for one asset, Plus at $38/month for up to 3 assets, and Professional at $73/month for up to 7 assets.
- AirWatch. This app and device security software offers 4 pricing suites that start from $3.78/device/month up to $20/device/month. Prices are slightly higher for plans based on per user.

BigID helps you discover, manage, and protect your business’ critical data using modern data intelligence platform.
Potential Issues
There is no foolproof security software to completely protect you from cyber threats. Identifying potential issues you might encounter beforehand can help you prepare and plan steps to solve them before they happen. Below are some examples to take note of:
- Need for more than one software. Depending on your requirements, you may need to install more than one software program to address all your cybersecurity needs. For instance, installing antivirus software does not prevent you from getting hacked because it is not a firewall. This can be mitigated by identifying your IT infrastructure, organization setup, existing software systems, and potential cyber threats. By understanding your specific business environment, searching for the right and complete solution can be easier as your choices are narrowed down.
- Accessibility poses risks. Accessibility offered by software products poses both a benefit and a risk. When your systems live on software, anyone can access it with the right login details and information. Hence, security software with role-based access is available to control and limit the access of your employees and contractors. Employing network monitoring and web filtering technology, as well as educating your employees, is essential.
Latest Trends
After understanding what is IT security software, we can now take a look at where it’s headed. As the tactics of cybercrime evolve, security vendors must continuously innovate and improve their products. Here are some of the software’s latest trends:
- Application of blockchain principles. To face the increasingly sophisticated cyber threats, an emerging approach such as the blockchain principle provides a promising leap forward in strengthening information protection. Using blockchain technology, data is stored in an open space ledger that’s decentralized in a distributed manner. This increases the difficulty of mass data hacking and tampering since all participants of the blockchain network can immediately see if the ledger is modified in any way.
- CARTA approach. The Continuous Risk and Trust Assessment (CARTA) is a new approach for a continuous, regular review of users. Basically, this process uses a real-time assessment of risk and trust in an IT environment. For example, only when a user poses a minimal risk of privilege abuse – as carefully studied – can they be granted extended access rights. This method aims to administer informed decisions regarding security posture for companies.
- Tailor-made security. Security vendors are now engaging a more personalized approach to security by considering each organization’s IT infrastructure, industry, complexity, size, and budget in order to address common pain points in a more targeted way. This provides organizations with more effective solutions as the approaches are tailored to their requirements.
Never underestimate the threat
In 2018 alone, there were 21 instances where millions of user accounts and customer personal information were compromised because of security breaches on large businesses and corporations including Facebook, British Airways, T-Mobile, Cathay Pacific, and Marriot Hotels, among others. A year earlier, Yahoo reported that data involving 1.5 billion accounts were hacked. What do these tell us? Even global corporations with the most stringent cybersecurity measures are not safe. How much more with smaller companies and businesses?
Here are some more alarming cyber-threat statistics:
- Nearly 800 million attacks launched from online sources across 194 countries were blocked by Kaspersky Lab.
- In Q1 2018, the same cybersecurity company detected 1.3 million malicious installation packages downloaded on mobile devices.
- There are over 282 million unique URLs that have been identified as malicious.
- More than 200,000 computers were infected by malware designed to steal money through online access to bank accounts.
In today’s digital world where financial transactions are done online, important information is stored in the cloud, and connected devices are linked not only to the internet but also with each other, the need for defensive and protective tools is paramount. You should not downplay the existing and potential threats. You may say yours is just a small business that won’t attract the attention of hackers. Don’t be complacent. Hackers go for the most vulnerable. It has been found that 43% of cyber attacks targeted small businesses. The more should you be on your toes because if these attacks can hit hard some of the biggest corporations, yours may not survive the impact. Take proactive and preventive steps, and seriously consider investing in robust IT security software that can safeguard your systems, devices, and most precious data.
Key Insights
- Definition and Importance: IT security software is crucial for protecting businesses’ computers and networks from unauthorized access and cyber threats. It is essential for safeguarding sensitive information and managing core operations.
- Types of IT Security Software: Key types include firewalls, antivirus software, spyware detection, and password protection, each targeting different security threats.
- Key Features: Important features include automatic updates, real-time scanning, auto-clean, multiple app protection, and user-specific data sources to ensure comprehensive protection.
- Benefits: IT security software prevents viruses and identity theft, protects valuable information, ensures compliance with legal standards, provides client security, and reduces development costs.
- Buying Considerations: When selecting IT security software, consider a layered security approach, compatibility with system needs, and the ability to cope with emerging threats.
- Examples of IT Security Software: Notable solutions include Trustifi, ManageEngine, BigID, Norton, Cloudflare, Avira, Malwarebytes, Kaspersky, Spiceworks, Webroot, Bitdefender, and AVG.
- Pricing: Costs vary widely based on features and company needs, with options ranging from free versions to premium packages.
- Potential Issues: Businesses may need multiple software solutions to cover all security needs, and increased accessibility can pose additional risks.
- Latest Trends: Innovations include the application of blockchain principles, the Continuous Risk and Trust Assessment (CARTA) approach, and tailor-made security solutions for specific business needs.
- Cyber Threats: Cyber threats are evolving and can affect businesses of all sizes, highlighting the need for robust cybersecurity measures.
FAQ
- What is IT security software? IT security software protects computers and networks from unauthorized access, cyber threats, and potential data breaches. It includes tools like firewalls, antivirus programs, and spyware detection systems.
- Why is IT security software important for businesses? IT security software is vital for safeguarding sensitive information, managing core operations securely, and protecting against cyber threats that can lead to data breaches and financial losses.
- What are the different types of IT security software? Key types of IT security software include firewalls, antivirus software, spyware detection tools, and password protection systems. Each type targets specific security threats to provide comprehensive protection.
- What features should I look for in IT security software? Important features to consider include automatic updates, real-time scanning, auto-clean, multiple app protection, application-level security, and user-specific data sources.
- How does IT security software benefit my business? IT security software prevents viruses and identity theft, protects valuable information, ensures compliance with legal standards, provides client security, and reduces development costs by preventing data loss and retrieval expenses.
- What factors should I consider when buying IT security software? Consider a layered approach to security, compatibility with your system needs, and the ability to cope with emerging threats when selecting IT security software.
- Can you provide examples of IT security software solutions? Notable IT security software solutions include Trustifi, ManageEngine, BigID, Norton, Cloudflare, Avira, Malwarebytes, Kaspersky, Spiceworks, Webroot, Bitdefender, and AVG.
- How much does IT security software cost? Pricing varies widely based on features and company needs, with options ranging from free versions to premium packages that can cost several hundred dollars annually.
- What potential issues might I encounter with IT security software? Potential issues include the need for multiple software solutions to cover all security needs and the risks posed by increased accessibility to the system.
- What are the latest trends in IT security software? Latest trends include the application of blockchain principles for data protection, the Continuous Risk and Trust Assessment (CARTA) approach, and tailor-made security solutions for specific business needs.
- How serious are cyber threats to my business? Cyber threats are evolving and can affect businesses of all sizes. Even small businesses are frequently targeted, making it essential to invest in robust cybersecurity measures to protect against potential attacks.


























Leave a comment!