The best email encryption solution in the market is Trustifi. It provides businesses with an integrated encryption solution for desktop, mobile, and gateway connections. It hosts a compact set of tools for email encryption and fraud detection. It also comes equipped with compliance management and policy management modules. With these tools at your disposal, you can minimize the risks of attacks and enhance data security.
Email encryption software helps protect businesses from data theft and malicious attacks leading to unwanted fines, sanctions, and loss of stakeholder relationships. Since email communications are not secure by default, the software works by embedding a coding scheme to the data to make the data set complex and unreadable. Email encryption can be a part of an email management software or a standalone tool, as what we’ll be presenting below. You need to choose a solution that is intuitive, reliable, comprehensive, and user-friendly.
In this guide, we present to you the 12 best email encryption software in the industry. Our team has selected many of the popular brands based on comprehensibility and reliability in features, brand presence, pricing, and integration.

What is the best email encryption software?
There has been a rapid growth in the demand for cybersecurity tools. It is forecasted that by 2021, cybersecurity software costs will reach the $6 trillion mark, according to Forbes. It is also estimated that around 230,000 malware samples are developed daily. While there is a consistency in the development of tools for countering these attacks, there is still a lot to do in terms of mainstreaming the benefits and importance of cybersecurity measures. And, there is no other perfect time to do so. A report by the University of Maryland estimates on the frequency of cyberattacks that hacker attacks occur every 39 seconds on average.
While you may think that these hackers are after larger and medium-sized businesses that store more voluminous amounts of data, small businesses are just as open to attacks. All in all, 65% of cyber attacks target small and medium-sized businesses. These attacks consist mostly of web-based, phishing and social engineering, and service attacks.
Data from Accenture and Ponemon Institute reports that the U.S. suffered greatly from cybercrime, costing it around $27.37 million in 2018.
Source: Accenture, 2019
Without the full deployment of a cybersecurity system, businesses have millions to lose in the long run. A report on data breach costs for 2018 by IBM projects that U.S. businesses are expected to lose $7.91 million on average. To add insult to injury, the process of identifying and processing a data breach normally takes 196 days.
By investing in robust cybersecurity software, you can help protect your devices, business information, and other data assets. If you’re into safeguarding your business across all fronts, you may study what types of security software your business needs. Read further to see the best email encryption software and consider each one based on specifications and requirements.
12 Best Email Encryption Software
1. Trustifi

Trustifi is a cloud-based security software designed to protect email communications. With features such as two-factor authentication, email quarantine, military-grade encryption, fraud detection, and single sign-on, this platform can help you make sure that your inbound and outbound messages are completely safe.
Using this platform, businesses can also perform compliance management and policy management. These allow you to set security standards within your organization as well as ensure that all emails in your system automatically comply with regulatory compliance guidelines.
Aside from the abovementioned functionalities, Trustifi also has a powerful optical character recognition (OCR) feature powered by machine learning. This allows the platform to quickly scan email attachments and encrypt sensitive data. From there, it can categorize attachments based on their level of sensitivity without the risk of data loss.
Another unique Trustifi feature is its patented email postmarking technology. With this at your disposal, you can provide legal proof that your emails are sent and opened by recipients. This makes it simpler to track email data.
Trustifi is supported through a variety of web browsers. It can also integrate seamlessly with Microsoft 365 and Google Workspace apps.
The vendor currently only offers this software by quote so be sure to get in touch with a representative for more information.
Detailed Trustifi Review
2. Symantec Gateway Email Encryption

Symantec Gateway Email Encryption delivers essentially managed, standards-based email encryption to secure email communications. The software functions as a firewall from unauthorized access over the public Internet regardless of whether or not the recipients own an email encryption tool or not. This enables organizations to minimize the risk of a data breach with compliance to the regulatory ordinance for security and privacy of information. The software presents functions for web email protection, PDF email protection, and gateway-to-recipient security.
Web email encryption is used when the recipient doesn’t own encryption software for emails. To provide the necessary secure communication between the sender and receiver, the recipient receives an email with a link to a web portal. The user logs into the portal to access the email and respond with the utmost security. This way, all email communications take place within an encrypted environment. It is an ideal solution for secure collaboration.
When dealing with one-way communications, PDF email protection is especially useful. The email is sent as an encrypted PDF attachment wherein the recipient can only access the information with a user-defined password to decrypt it. This solution is ideal for sending secure information when no response is required.
Gateway-to-recipient is commonly used when one organization communicates with another organization that has an encryption tool in place. This is effective when both organizations are using compatible methods.
Symantec Gateway Email Encryption is supported through these web browsers: Microsoft Internet Explorer® 9 to 11, Microsoft Edge, Mozilla Firefox® 38.4.0 ESR, 42.0, 53.0, and Apple Safari® 8, 9.
The software is offered through quotation.
3. Trend Micro

Powered by XGen, Trend Micro Email Security focuses on protection, detection, and response when dealing with security threats like ransomware, fraud, and targeted attacks. The software provides tools to detect internal threats within the organization. It is capable of sharing threat intelligence with other security layers that allow its customers to access email and collaboration systems to detect existing malware or compliance violations within the organization.
You may also look into how you can work with integrated communication software systems to enjoy greater efficiency and collaboration within your business.
Trend Micro delivers absolute security against threats in disguise. XGen security uses cross-generational defense techniques to precisely detect the widest range of email attacks and delays in the delivery of legitimate emails. In multi-stage attacks, an employee’s device or credentials can be compromised leading to phishing of emails internally.
The software can respond and remediate effectively as it helps with the discovery and cleanup of malware activities through multiple security layers.
Trend Micro offers a wide range of solutions to fit every environment and situation. The software offers email gateways as a cloud service, virtual appliance, or hardware appliance.
No pricing plans are displayed on the website. The solution is offered through quotation.
4. Micro Focus SecureMail On-Premises

Micro Focus Voltage SecureMail is an end-to-end email encryption solution that is widely used in maintaining Personally Identifiable Information (PII) and Personal Health Information (PHI) secure and private. One of the core features of this solution is the identity-based encryption that enables organizations to make use of secure communications without downloading any software. Information can be sent even if the recipient is offline with the use of unique private keys.
Micro Focus Voltage SecureMail On-Premises also covers two major features. SecureMail On-Premises Standard provides a full scope email encryption solution available for desktop, cloud, and mobile. It is ascendible to countless users leveraging stateless key management and offering diverse advanced add-ons.
On the other hand, SecureMail On-Premises Enterprise is a global enterprise email encryption solution with considerable add-on features and customized user experience that includes custom branding and multi-language support.
The vendor does not include the pricing plans and information on its website. The software is offered through quotation.
5. Tutanota

Tutanota is an email encryption service that provides a free version for personal use and/or a fully-featured secure business email service for enterprises. All basic secure email account in Tutanota is always free with all security features included. No personal information is required to access an anonymous email account. The service does not log IP addresses and removes IP addresses from every email communication and encrypts the subject, content, and all attachments of emails. Only the user can decrypt and access data. It also features an address book where a user’s contacts can be imported with confidentiality and security.
Tutanota is available on desktop web browsers and it has native apps for Android and iOS.
A private account in Tutanota is free of charge. However, it is upgradeable to Premium (€1.20/month) and Professional (€6/month) to add more features that expand the user’s security and accessibility. Business accounts are only available in Premium and Professional accounts with the same price range and features. Tutanota provides special offers for additional storage for secured emails and additional email aliases.
6. Proofpoint Email Encryption

Proofpoint Email Encryption delivers automatically-encrypted messages and attachments. Users are not required to manually encrypt their email to send and receive secure messages. The service provides powerful, policy-driven encryption features that reduce the risks concerning regulatory violations, data loss, and corporate policy violations. Proofpoint Email Encryption is ideal for any enterprise that requires sensitive data security that can still be accessible to appropriate affiliates, business partners and end users—available on desktops and mobile devices. Proofpoint Email Encryption offers several functions such as policy-based encryption, streamlined storage, and granular control.
The policy-based inscription provides automatic encryption that is relative to an enterprise’s policies. This function focuses on consistent and accurate compliance, data loss prevention and content security policies.
Under streamlined storage, burdens in key management, backup, and administration are eliminated through Proofpoint Key Service. It offers secure, cost-efficient, highly available and fully redundant key storage facilities.
Another function of the Proofpoint Email Encryption is providing a granular message control by permitting encrypted messages’ expiration and the capability to revoke any message to any recipient.
The vendor does not include the pricing plans and information on the service on its website.
7. Egress

The software helps secure unstructured data to reach compliance requirements and manage business efficiency. The company has AI-powered platforms that let users control and secure data. Egress is trusted by enterprise organizations and governments around the globe. The platform offers email and document classification, accidental send prevention, email encryption, secure online collaboration, audit, and compliance reporting.
Egress Email Encryption provides easy encrypted email communication. Users can secure emails with one-click; send large files securely by surpassing file size restrictions with complete control over who has access; revoke further access to any content the user sent; and avoid data breaches and fix errors. Egress Email Encryption covers functions for real-time control sharing sensitive data, Egress smart authentication, and flexible hosting options for secure mail infrastructure.
Real-time control when sharing sensitive data allows the users to protect data however they need to, prevent downloads and copy/paste, audit data sharing and view access reports, customize email security policies and automation, and secure data relative to the actual risk of a data breach.
Egress provides diverse pricing plans depending on the number of software users. For single users of 1-4, the service is available for £80/user/year; and for singles users of 5-9, the service is available for £60/user/year. For business packs of 10 users, the rate is £50/user/year. However, for business packs of 20, customers are advised to contact the vendor.
8. Virtru

Protect, share and control are the main factors that could describe Virtru Email Encryption solution. It allows users to merely “flip a switch” to enable end-to-end encrypted email communications within existing applications such as Gmail and Microsoft Email. The on-demand encryption solution ensures smooth navigation and enhances security awareness for its users.
Virtru permits its customers to revoke, expire and track or disable forwarding—even after the messages have been read and forwarded so the users never lose control of their sensitive information. Another feature of the product is its centralized enterprise policy management. This allows its users to set, enforce and report on DLP policies (also known as email transport rules) in an incorporated administrative console.
The software also grants its users to quickly see where the emails and files have been shared, whether it is inside or outside the organization. Additionally, custumer-hosted keys give the users complete control over protected content. This prevents unauthorized access and blind government subpoenas.
Pricing plans and packages are not presented on the website.
9. VMware Workspace ONE Boxer
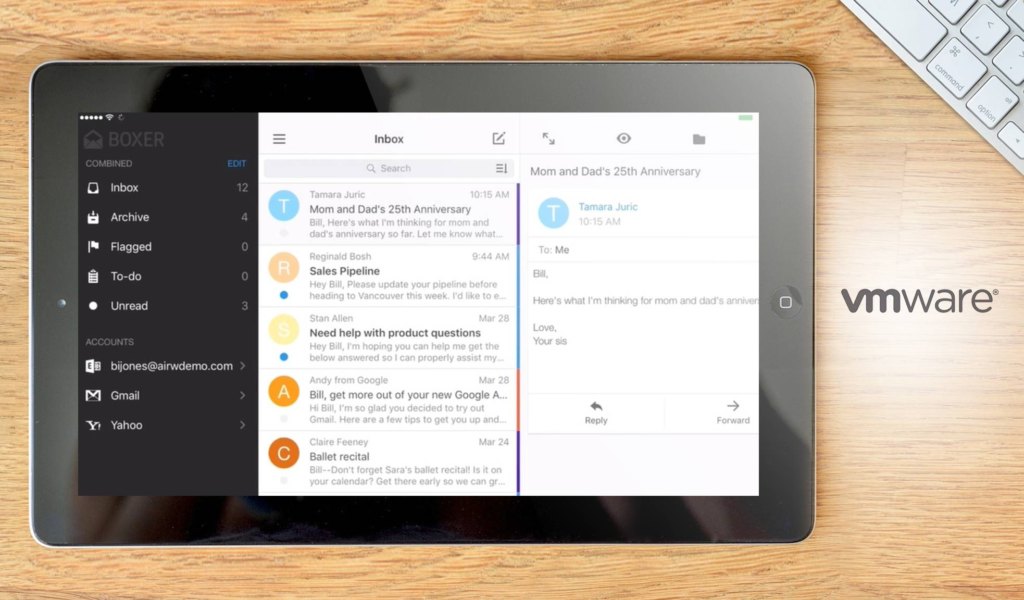
VMware developed a faster and smarter mobile inbox that can be easily configured by its users. It has tools such as custom swipe gestures and quick-reply templates, quick sharing of calendar availability and more. Workspace ONE Boxer is an efficient way to manage emails. The application offers a consumer-centric focus on mobile efficiency with AES 256-bit encryption.
Boxer has configurable swipe gestures that allow its users to tailor email experience for fast management on-the-go. Likewise, one of its features makes use of templates to quickly respond to emails. It also lets its users send their availability within the time of the month or year using the calendar.
Workspace ONE Boxer is available on Google Play Store for Android users and Apple Apps Store for IOS users. The application is free of charge.
10. Folder Lock
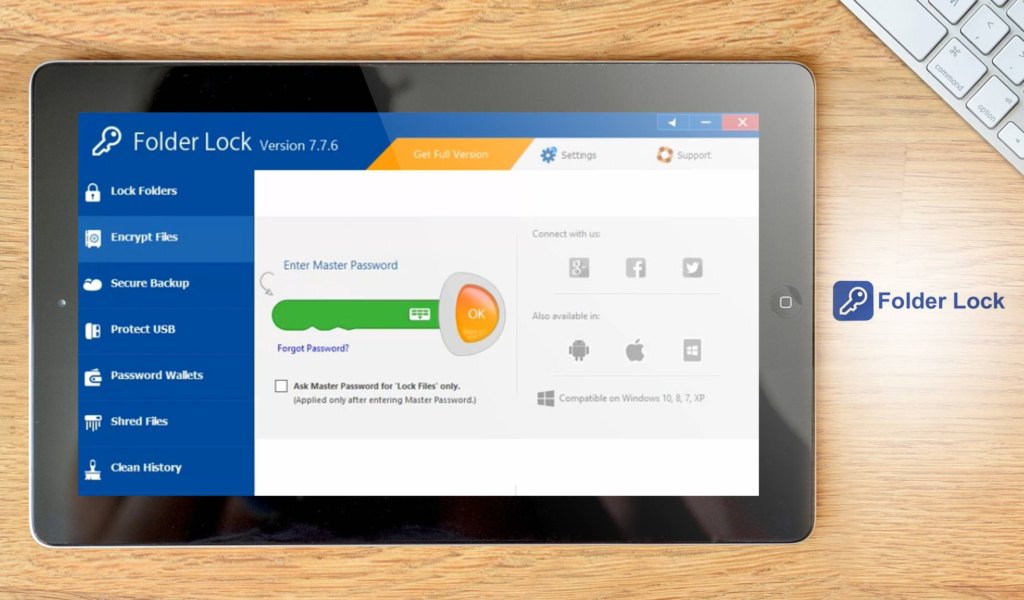
Folder Lock offers password-protected files, folders, and drives; file encryption and real-time backup; portable driver security; and files and drives shredding and history cleaning. The software is the most downloaded file-security application. It has 45 million users.
The software can lock and hide files and folders within a short span of seconds. It allows its users to protect their files with password and confidentiality features. Folder Lock’s encryption feature is run by AES 256-bit encryption. Users don’t need to encrypt or decrypt files when accessing. The software provides 2-way encryption and backup method, letting its users back up encrypted ‘Lockers’ online. This feature does not only secure the files from a data breach but also from loss or damage.
Users can keep their encrypted ‘Lockers’ in portable devices such as USBs and external drives. Folder Lock changes these ‘Lockers’ into executable files so that the installation of the software is not needed every time the secured files are accessed. Folder Lock also makes use of password wallets where digital wallets can be created to secure confidential financial information. This information is automatically encrypted when saved. The shredding feature allows users to permanently delete files and folders that results to non-recovery.
Folder Lock Software works on 32-bit and 64-bit Windows 10, 8, 7, Vista and XP.
The software can be availed at $39.95.
11. AxCrypt
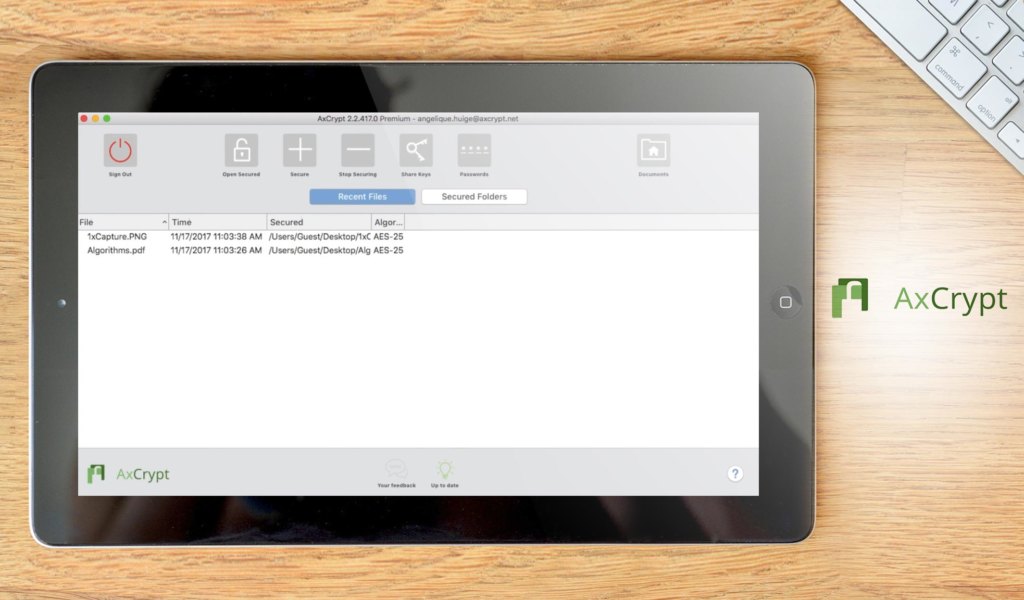
AxCrypt is one of the world’s most popular encryption software. It provides individuals and small organizations with encryption solutions that are easier to navigate. Axcrypt aims to remove the complexity from the utilization of strong and proven cryptographic technology.
The software provides strong security with 256-bit encryption. It is the most standardized encryption available and mostly used for top secret information all over the world. In sharing a protected file made from the AxCrypt software, the recipient only needs a free AxCrypt ID and will be invited via email. The invitation email contains directions with regards to viewing and editing the file. AxCrypt supports several languages such as English, Dutch, French, German, Italian, Korean, Portuguese, Spanish, Swedish, Turkish, and Russian.
AxCrypt is available for free with very minimal to no features but viewing. Premium membership (for individuals) costs $36.00 per year and Business membership (for organizations) costs $89.00 per year.
12. Sendinc
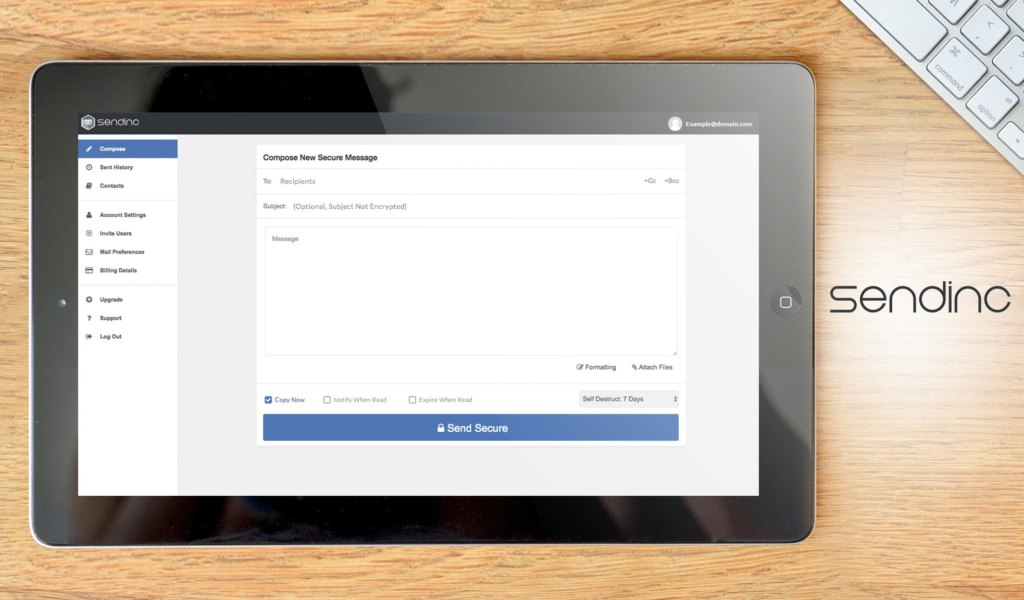
Sendinc guarantees that emails delivered through their service are encrypted to the highest standards. It requires no software for its customers. Any existing email address can be used upon registration. Sendinc does not store encryption keys, ensuring that emails are only decrypted by the recipients.
The service allows its users to send emails and attachments with up to 10 MB. Sendinc operates on 256-bit SSL encryption. The messages are automatically deleted 7 days after sending on free accounts. However, in order for the recipients to view the encrypted email, they need to sign up to Sendinc. The service operates without any downloadable software. This is beneficial for users to send secure emails from any device.
Sendinc is available in web browsers and supports iOS and Android.
The service is available for free with limited features. It offers a pricing plan of $48.00 per year for individuals (Pro) and $48.00 per year (per user) for businesses (Corporate) with 5 licenses available.
Select the solution that fits your specific needs
Prior to picking your chosen software, ensure that you take the crucial step of contacting the vendor and going the free trial or demo route. Consult with the vendors and familiarize yourself with the overall feel and system of the aforementioned software.
It is also worth noting that email encryption and management go hand in hand. Look at email management tips so you can review the software’s suitability to your business model.
Email encryption is also sometimes complemented or included/integrated with file sharing software. For example, Encyro, offers small and medium-sized businesses with email protection, quick file attachment access, and audit trails.
In evaluating the list of software to choose from, carefully consider the scope of the encryption and security and protection modules. Understand comprehensively the infrastructure and system built for a solution. A good example is Symantec, which gives users an end-to-end integrated system for ensuring data security on mobile, web and gateway connections.
Also, determine the type of information you seek to protect and safeguard from cyber attacks. Some solutions are tailored better for particular sectors or industries. Micro Focus, for instance, focuses on securing personal identifiable and health information.
Lastly, look into how scalable and expensive the solution is. Some of the solutions listed offer flexible pricing plans specifying the number of packs or individuals covered. As your business expands, so do your security needs, so meticulously evaluate how scalable the solution is.
Scrutinize the solution you will secure for your business. Of course, it won’t hurt to know some helpful fraud prevention strategies for your business.
Key Insights
- Rising Cybersecurity Demand: The rapid growth in cyber threats and data breaches has significantly increased the demand for robust email encryption solutions, with the cybersecurity market projected to reach $6 trillion by 2021.
- Frequent Cyberattacks: Cyberattacks occur every 39 seconds, highlighting the urgent need for effective email encryption to protect sensitive business communications from data theft and malicious attacks.
- Small Business Vulnerability: While large enterprises are often targeted, 65% of cyberattacks are directed at small and medium-sized businesses, emphasizing the importance of email encryption across all business sizes.
- Cost of Cybercrime: Cybercrime costs are substantial, with the U.S. alone suffering an estimated $27.37 million in damages in 2018, and businesses potentially losing $7.91 million on average due to data breaches.
- Comprehensive Solutions: Effective email encryption solutions should offer features like two-factor authentication, automatic encryption, compliance management, and integration with existing email platforms to ensure comprehensive protection.
FAQ
1. What is email encryption software and why is it important?
Email encryption software is a tool that protects email communications by encoding the data, making it unreadable to unauthorized users. It is important because it helps prevent data breaches, protects sensitive information, and ensures compliance with regulatory standards.
2. How does email encryption work?
Email encryption works by converting the contents of an email into a coded format that can only be decrypted and read by the intended recipient. This process typically involves the use of encryption algorithms and keys to ensure data security.
3. What are some key features to look for in email encryption software?
Key features to look for include two-factor authentication, automatic encryption, policy management, compliance management, optical character recognition (OCR), email postmarking, and integration with existing email platforms like Microsoft 365 and Google Workspace.
4. Can email encryption software be used on mobile devices?
Yes, many email encryption solutions offer mobile compatibility, allowing users to secure their email communications on smartphones and tablets. Solutions like Trustifi and Tutanota have native apps for Android and iOS.
5. How does policy-based encryption enhance email security?
Policy-based encryption automatically encrypts emails based on predefined policies set by the organization. This ensures consistent and accurate compliance with security standards and reduces the risk of human error.
6. What are some popular email encryption software options available?
Some popular email encryption software options include Trustifi, Symantec Gateway Email Encryption, Trend Micro, Micro Focus SecureMail On-Premises, Tutanota, Proofpoint Email Encryption, Egress, Virtru, VMware Workspace ONE Boxer, Folder Lock, AxCrypt, and Sendinc.
7. How do email encryption solutions handle attachments?
Many email encryption solutions, like Trustifi and Egress, offer features to encrypt email attachments automatically. This ensures that sensitive data within attachments is protected from unauthorized access.
8. Are there free options available for email encryption?
Yes, there are free options available for email encryption, such as Tutanota, which offers a free version for personal use. However, these free versions may come with limited features compared to their premium counterparts.
9. How can email encryption software ensure compliance with regulatory standards?
Email encryption software ensures compliance by providing tools for policy management, automatic encryption, and detailed reporting. These features help organizations adhere to regulatory requirements for data protection and privacy.
10. What are some common challenges businesses face with email encryption?
Common challenges include the complexity of setup and management, ensuring compatibility with existing systems, training employees to use the software effectively, and balancing security with ease of use. Choosing a user-friendly and comprehensive solution can help mitigate these challenges.
























Leave a comment!